As this part of equipment - actually an excellent example of intersection between IT, IT Security, Cybersecurity and Information Security also - may often be overlooked when it comes to securing (a)n (corporate, SoHO) environment, as it - among other things - may pose both an ingress point of an attack and an egress point of data (document) exfiltration, I've decided to write an article about (re-)configuring it properly or hardening it, including some reasoning behind it, i.e. with some tips and remarks gathered by doing just about that on a non-corporate example of a SoHo multi-functional device coming from Epson (Seiko Epson Corp.).
Given the range of services and functionalities available on the device (which may depend on the local market, product registration, firmware installed etc.), such as:
- Wi-Fi Direct
- Epson Connect Services
- Google Cloud Print Services
- AirPrint (a feature from Apple enabling quick, driverless printing from iPhone, iPad, Macs, and Apple Vision Pro, i.e. from operating systems such as macOS, iOS, and iPadOS)
- PC-FAX
- etc.
I've decided to tackle this topic roughly by:
- Applying the latest firmware update (CAUTION: depending on the model, you might lose your previous settings, therefore try to back these up before proceeding - if nothing else, then by taking screenshots, printing the previous configuration out and / or downloading the files showing the settings!);
- Reconfiguring authentication, i.e. by restricting access to management interfaces;
- Checking, i.e. disabling unused services (i.e. by doing ASR - Attack Surface Reduction-related work focused on services themselves); all of the above also due to the fact that such a device typically may not necessarily support 2FA/MFA.
A few interesting remarks and tips how to conduct these changes can be found below:
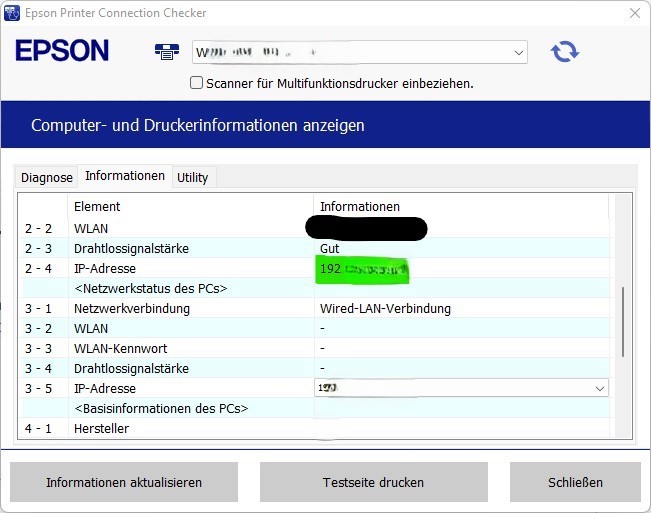
For the access to the configuration GUI this time a W(ireless)LAN (not a usually more secure cabled LAN, which is usually strictly required for the 1st device setup) has been used.
The device should be accessible (via almost any modern browser) at the address marked green below.
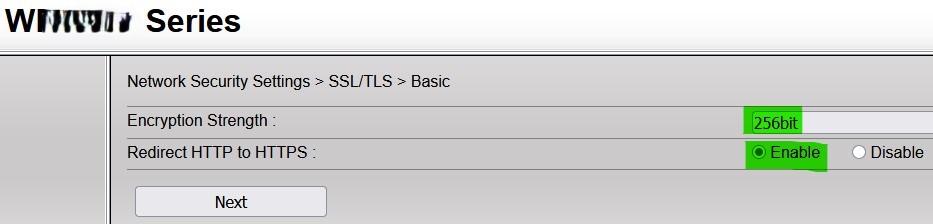
It's important to notice that - by default (during the initial device setup via a LAN cable) - HTTP was used (no HTTPS was required; which exactly is the reason why the vendor was insisting on using a LAN cable to configure it), so this is the 1st thing to check - whether HTTPS (i.e. redirection from HTTP to HTTPS) is now forced, i.e. to check whether the default values (after a cable-based configuration) are still (stuck) there.
This can be done by accessing (a separate) Admin. Login part, i.e. Advanced Settings section.
The check / reconfiguration can be made under "Network Security Settings" - "SSL/TLS" - "Basic", where something like this should be shown (the strongest encryption set and the "Redirect HTTP to HTTPS" option enabled):
Only after HTTPS has been configured, it's very advisable to change the (more permanent) administrator password.
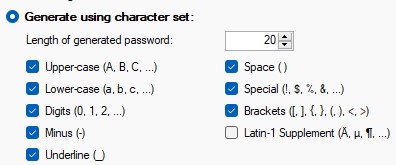
This device does support the following password length / complexity - as always (particularly if no 2FA/MFA is available), I'd suggest to go with the highest settings that the system can accept (IMPORTANT NOTICE: just make sure that it really works, as I've seen devices also which - as hard as it may be to believe - don't have input validation, i.e. they don't check whether the password entered is actually valid for the device, rendering the access impossible, i.e. basically requiring a full system / hard reset after you've already through with the whole configuration):
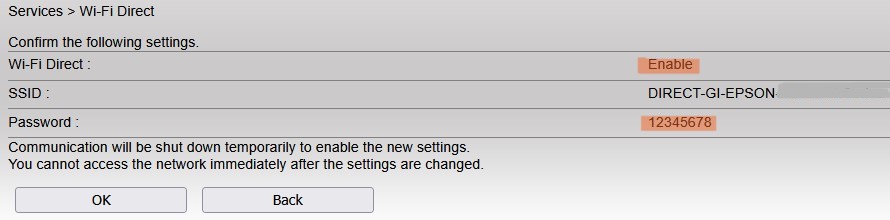
 In this context it's also important to notice that the GUI doesn't seem to able to mask the password(s) being entered (such as the one for Wi-Fi Direct), therefore be careful where you're conducting a (re-)configuration.
In this context it's also important to notice that the GUI doesn't seem to able to mask the password(s) being entered (such as the one for Wi-Fi Direct), therefore be careful where you're conducting a (re-)configuration.
The next step(s) possible would include:
- disabling Wi-Fi Direct if it's not being used (or/and change the password while doing so, as the standard one is way too simple - please see below; the system does seem to be able to correctly handle 20 characters, incl. special signs correctly);
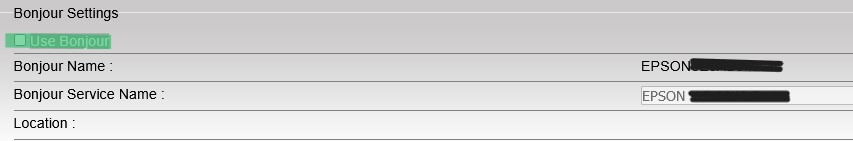
- disabling any other service which may not be strictly needed (particularly due to the fact that the picture above shows that there might be some improvement/s needed to the way this device is handling security-related settings) - such as Bonjour (aka mDNS - for Apple devices - displayed below), PC-FAX etc.:
- setting the power saving settings more restrictively (depending on the typical usage scenario) may also - besides saving some energy - give you an additional layer of security (as what isn't there, can't be misused or attacked either).
At the end, adding a CA-signed certificate (instead of a self-signed, vendor-provided one; produced by using the built-in CSR-generating functionality might give you additional certainty).